
VPN for Businesses: Is It Important?
A virtual private network (VPN) lets you access parts of the internet anonymously by establishing an encrypted tunnel. VPNs provide enhanced security without affecting convenience

A virtual private network (VPN) lets you access parts of the internet anonymously by establishing an encrypted tunnel. VPNs provide enhanced security without affecting convenience
Cybercrime is on the rise, and the scary part is that threat actors are improving in sophistication and efficiency. Although cyber attackers will use every

Cyber network security is the most crucial part of every modern business. Regardless of your business’s nature of operations, you need cybersecurity to protect sensitive

Ransomware attacks remain at a near-record high, and given the ever-increasing digital surface of businesses, it’s harder than ever to stay protected. It doesn’t help

The ever-increasing demand for digitalization in businesses has created more opportunities for employees and business leaders than ever before. Modern enterprises operate in a dynamic

Nearly every business that has undergone digital transformation essentially has an expanded attack surface that puts them at a great risk of cyber-attacks. Lately, remote

Data loss not only disrupt productivity for a short period of time but also leads to more permanent problems such as reputational risk, bankruptcy, closures,
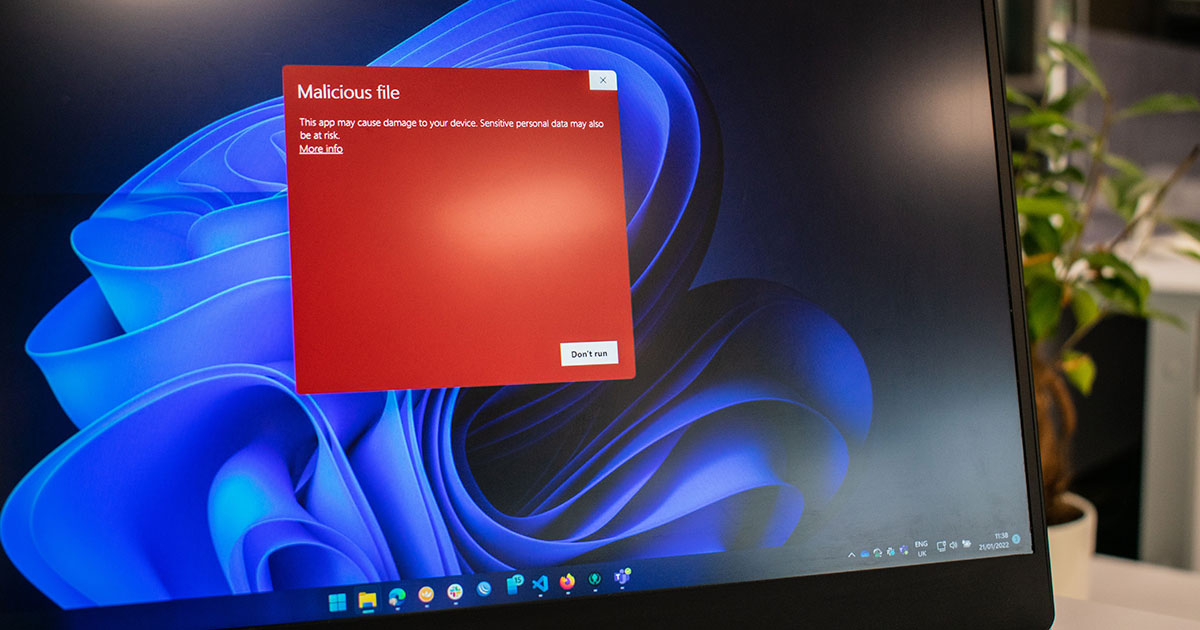
Data security is the core of any business around the globe. Any threat to confidential data can lead to a series of serious problems. Malware

In the context of countless data breaches that have made news headlines in recent years, the old adage, “prevention is better than cure,” definitely applies

Reports of cybersecurity breaches have saturated the news and media. Every day, we wake up, shake our heads over reports of another data breach, and

What is communication security and why it is important? Security is no longer an option in the digital world. With so much data being sent

Cybersecurity professionals continue to defend businesses and networks from different types of threats. Cyber-attacks target thousands of businesses and private users every day. The primary